Cyber security analytics involves many tools. These include algorithms, statistical analysis, behavioural analysis, and machine learning (ML). These tools allow for faster and more efficient prevention and resolution of cyber security problems. Cyber security analytics is often a key component of a Security Operations Centre (SOC).
With hackers developing increasingly complex threats to steal sensitive information, cyber security has become a business-critical priority for enterprises. Gathering data about network vulnerabilities as well as any past and ongoing attacks is the best way to protect your business. This insight explores how cyber security analytics works and why it is a key tool for enterprises in the digital age.
What is cyber security analytics?
Cyber security analytics is an advanced approach to cyber security management enabling IT teams to prevent, track, and resolve attacks with scanning tools and data gathering tools that work with automation and ML. cyber security analytics is particularly useful in highly regulated industries such as healthcare and legal. This section looks at a few of the most common cyber security analytics tools.
SIEM tools
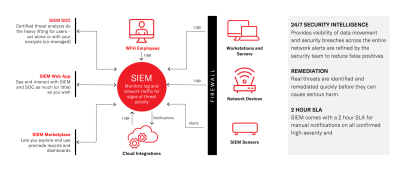
Security Information and Event Management (SIEM) solutions provide insights and alerts to identify potential threats and mitigate risks. A SIEM solution consists of different components involved in security information management (SIM) and security event management (SEM) including data aggregation, threat intelligence and advanced analytics, to name but a few.
SOAR tools
Security Orchestration, Automation, and Response (SOAR) tools are used for data gathering, analysis, and threat response.
NAV tools
Network analysis and visibility (NAV) tools analyse end-user and application traffic in real-time.
Threat intelligence tools
Impartial external companies generally provide threat intelligence tools and encompass different analytical processes to support cyber security data analytics.
UEBA tools
User endpoint behavioural analytics tools (UEBA) look for patterns to detect anomalies that might indicate or increase the risk of a cyber security breach.
Why is cyber security analytics important?
As cyber threats become increasingly complex, organisations struggle to protect their data and business-critical assets. Cyber security analytics offers 24/7 support tools that can not only detect threats in real-time but also establish a hierarchy of alerts and predict future attacks based on current data and behaviour. This significantly decreases the chances of a cyberattack, safeguarding your business and your stakeholders.
Assess your current level of protection
How does cyber security analytics work?
There are three main types of cyber security analytics, using ML to detect, log and fight threats:
Unsupervised anomaly detection
This type of ML aims to detect deviations from past behaviour. It is essential to tailor anomaly detection to the specific needs and behaviour of your organisation so as not to generate false positives. Anomaly detection models do not rely on past examples of attacks, so they are extremely thorough in identifying unknown threats.
Supervised detection
These systems use large quantities of data to learn the characteristics of specific threats and detect them. This type of ML requires training, so it will not be able to recognise unknown threats. For best protection, unsupervised and supervised anomaly detection should be used together.
Detection correlation
The detection outputs of supervised and unsupervised detection are commonly referred to as spot detections. Spot detections can provide information about single actions such as authentications.
They are useful to make predictions, but cannot offer an overview of attacks across the entire organisation. Detection correlation is used to fill this gap, as it allows IT security teams to form correlations between single-spot detections and get a complete overview.
Conclusion: protect your business with the power of cyber security analytics
Cyber security analytics is a key tool for enterprises to effectively neutralise cyberattacks. At ROCK, we provide our clients with customised cyber security analytics solutions. Our solutions collect data through 24/7 real-time network monitoring and leverage machine learning and artificial intelligence to detect suspicious activity.
Thanks to data logs, we take action to minimise risk, so you never lose your assets. If you want to save money, reduce risk and increase productivity, take a look at our cyber security services.